Have you ever wondered how the biggest brands in the world falter when it comes to data security? Consider how AT&T, trusted by millions, experienced a breach that exposed 73 million records—sensitive details like Social Security numbers, account info, and even passwords. Then there’s Ticketmaster, where over 560 million records were compromised, triggering a cascade of issues including an antitrust lawsuit from the Justice Department.
That’s not all: a single vulnerability in MOVEit led to 49 million records being compromised—impacting government agencies, financial institutions, and healthcare organizations alike, with damages soaring into the billions. And Dell? Their breach transformed personal customer data into a commodity traded on dark web forums.
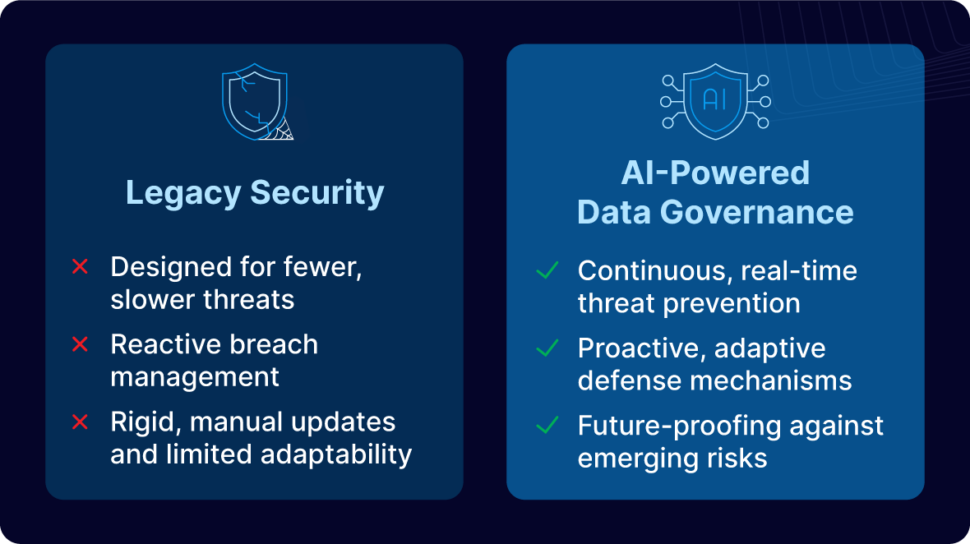
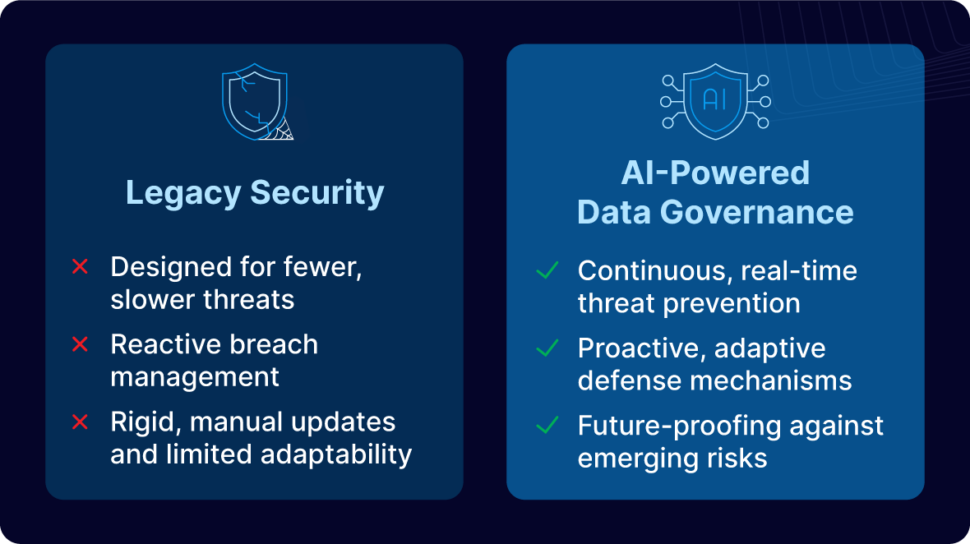
These incidents serve as a stark reminder that legacy data governance systems, built for a bygone era, are struggling to fend off modern cyber threats. They react too slowly, too rigidly, and can’t keep pace with the dynamic, sophisticated attacks occurring today, leaving hackable data exposed. That’s where AI-powered data governance comes into play.
In this blog post, we’re going to unpack the critical differences between legacy systems and AI-driven approaches, demonstrating why when it comes to hackable data, AI-driven data governance is the only way to go.
Why Proactivity Matters with Data Governance
When it comes to data governance, being proactive can mean the difference between keeping sensitive data secure or exposing it to the world. Cybercriminals target businesses that fail to act in advance. Proactivity enables businesses to:
Mitigate Breach Risks Before One Occurs
Every moment that hackable data remains unprotected, the risk of a breach increases. Legacy systems leave critical gaps between data creation and risk detection—gaps that cybercriminals can and do exploit. By contrast, Striim’s AI-powered data governance detects and classifies sensitive data in motion before it reaches storage. Additionally, Striim can encrypt, mask, or redact sensitive data all in real time, effectively preventing exposure.
Protect Brand Reputation and Trust
A data breach is more than just a technical failure—it can inflict irreparable harm on your brand reputation. Trust, once lost, is incredibly difficult to regain. Consumers expect their data to be handled with care, and any lapse in security can lead to significant financial and reputational damage. By implementing AI-powered governance, companies can demonstrate a commitment to real-time security, bolstering consumer trust and positioning themselves as leaders in data protection.
Streamline Compliance and Risk Management
Regulatory compliance isn’t just about avoiding fines—it’s about safeguarding trust. Legacy systems often struggle to meet evolving standards due to their reactive nature. In contrast, AI-driven solutions deliver continuous oversight, empowering organizations to adapt swiftly to regulatory changes and uphold rigorous risk management practices.
Striim’s platform serves as an ally on your path toward compliance, equipping your team with the tools needed to navigate an ever-evolving regulatory landscape.

The Future of Data Governance: Embracing the AI Revolution
The digital world is growing more complex every day, and so are the threats targeting hackable data. Legacy systems were designed for a different era—one with fewer threats and slower attack speeds. Today’s cyber threats are sophisticated, dynamic, and relentless. AI-powered data governance offers the agility and foresight necessary to stay ahead of these evolving risks, continuously learning and adapting to new attack vectors.
The move from legacy to AI-driven data governance represents more than just a technological upgrade; it’s a fundamental shift in how we protect our digital assets. Instead of reacting to breaches after they occur, AI-powered systems are designed to prevent them from happening in the first place. This shift not only enhances security but also supports a more robust, resilient infrastructure capable of withstanding the pressures of a digital-first world.
As data volumes explode and regulatory environments become stricter, the need for proactive data governance becomes ever more critical. Embracing an AI-powered approach is not just about addressing current challenges—it’s about future-proofing your organization against threats that have yet to emerge. By investing in continuous, real-time protection, businesses can secure their data, work towards compliance, and ultimately, preserve the trust of their customers.
Reimagine Data Governance with Sentinel and Sherlock: Striim’s AI Agents
Striim 5.0 introduces Sentinel and Sherlock, which redefine real-time data governance by seamlessly integrating advanced AI capabilities into your data pipelines. These intelligent agents ensure robust security without sacrificing system performance.
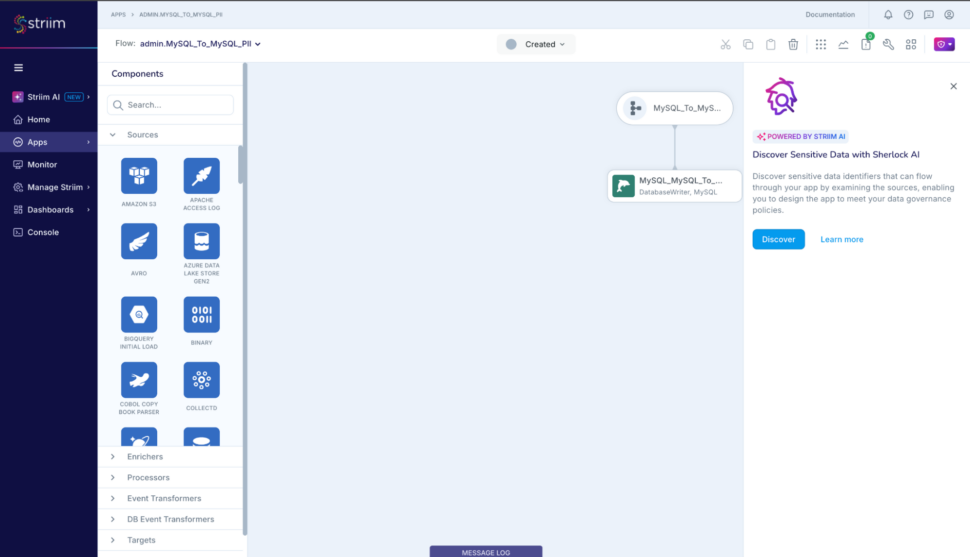
Sherlock AI: Proactive Source-Level Protection
- Early Identification: Detects sensitive data at the point of origin, even within third-party or SaaS-managed databases, before it enters your pipeline.
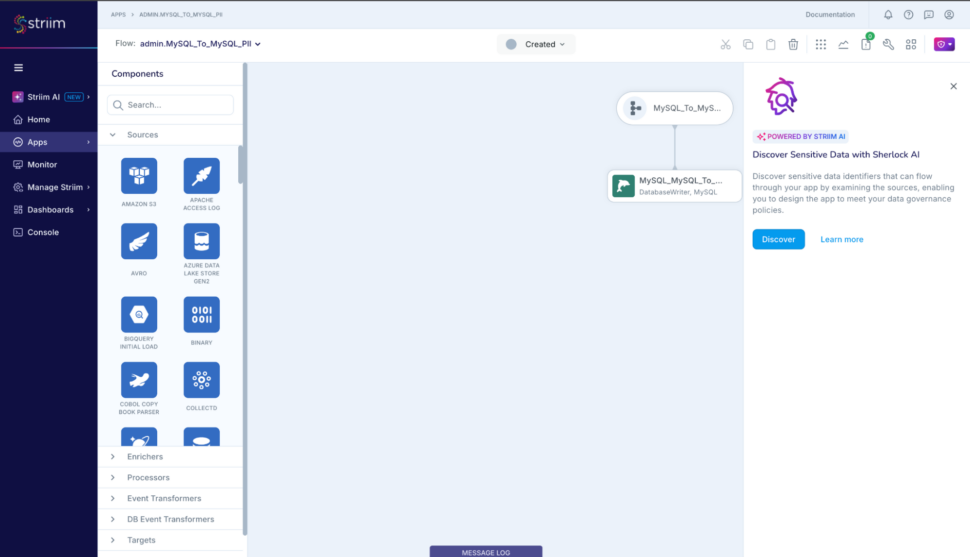
- Preemptive Risk Elimination: Finds and flags sensitive information before it’s in motion, reducing exposure risks from the outset.
- Holistic Coverage: Operates flawlessly across SaaS, cloud, and external systems, providing complete visibility into your data environment.
- Efficient Scanning: Uses lightweight processes that avoid impacting database performance.
- Automated Categorization: Instantly classifies financial, healthcare, and personal identity information, delivering real-time insights into data security.
- Quality Oversight: Monitors data integrity continuously, alerting teams when sensitive data appears where it shouldn’t.
Sentinel AI: Dynamic In-Motion Defense
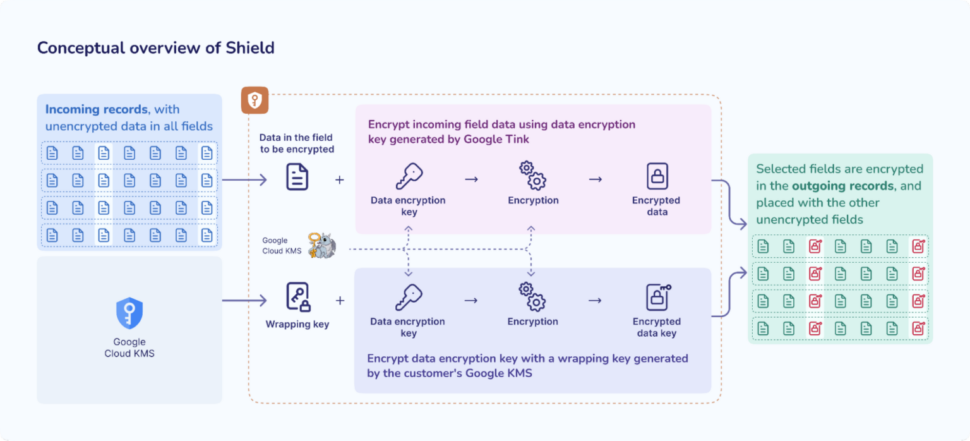
- Real-Time Protection: Monitors and secures sensitive data as it traverses your systems, ensuring constant vigilance.
- Precision Detection: Identifies personally identifiable information (PII) anywhere within a record—even if it’s incorrectly labeled—surpassing the limitations of traditional rule-based methods.
- Exposure Mitigation: Blocks unauthorized data transfers when moving information from internal systems to external analytics or sharing platforms.
- Compliance Coverage: Supports over 25 sensitive data types across multiple regions—including the USA, Canada, the UK, and India—to meet diverse regulatory needs.
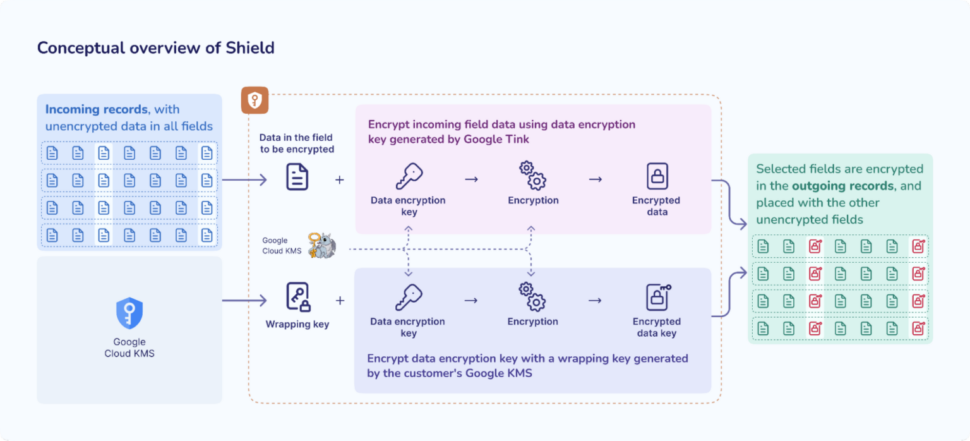
- Automated Response: Implements policy-driven actions such as encryption and various forms of masking (partial, full, regex-based) without manual intervention.
- Seamless Integration: Offers a plug-and-play user experience that allows for swift integration into existing data pipelines.
- Regulatory Alignment: Assists organizations in navigating compliance requirements such as GDPR, CCPA, HIPAA, and beyond.
Sentinel and Sherlock’s Unified Approach to Data Governance
The process kicks off with Sherlock AI, which scans both structured and unstructured data across SQL, NoSQL, SaaS, and cloud databases. It pinpoints and classifies sensitive financial, health, and identity-related data—helping to preempt issues before they occur.
Once the data is on the move, Sentinel AI steps in. Using sophisticated pattern recognition and natural language processing, it validates data in real time, catching errors traditional systems might miss. Based on predefined business rules, Sentinel automatically encrypts, masks, or blocks data transfers, ensuring that regulated information remains secure as it shifts between systems.
With continuous, real-time dashboards, Sentinel offers live reporting on data exposure, security interventions, and compliance status. It logs each event with AI-enhanced metadata for effective tracking and auditing, while its adaptive design accommodates evolving data sources through schema evolution.
This integrated, AI-driven framework not only keeps your organization audit-ready but also ensures full transparency into data protection measures. Furthermore, Sentinel’s compatibility with enterprise security tools like SIEM, DLP, Datadog, and Snowflake Security reinforces a comprehensive and unified security strategy.
Ready to take your data governance efforts to the next level? Try Striim today with a free trial or book a demo to see it in action.
Start Your Free Trial | Schedule a Demo